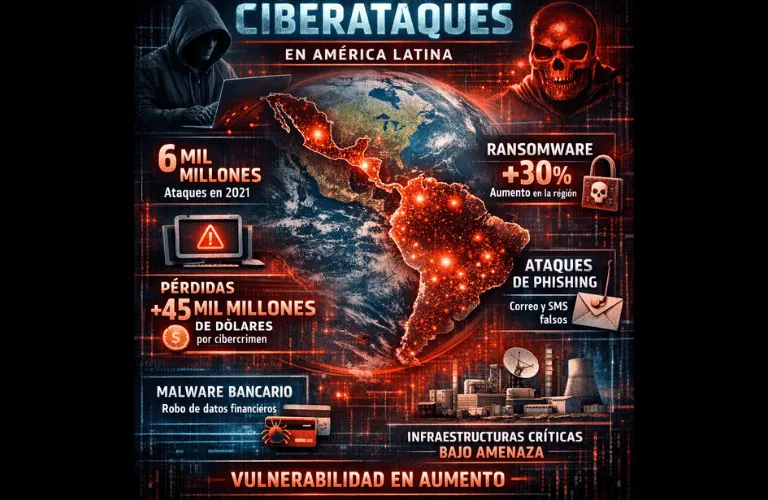
25% of Companies in Latin America Ciberattacked in 2025
By William Peña – Journalist, contributor at ITBS
Attacks are constant and never stop, while companies continue to believe “it won’t happen to me” … but it does.
The Security Report for 2025 highlights that one out of every four companies in the region suffered an attack last year. Most notably, 40% of those companies have no visibility whatsoever over their infrastructure. In short, they do not know whether they are being attacked or, worse, whether they have already been compromised.
Cybersecurity specialists agree that the likelihood of being attacked by hackers today is absolute. Added to this problem is the belief among company executives that their organizations are exempt from such attacks, when reality shows that the issue is not whether it will happen, but when and how — and, most importantly, whether they are prepared.
Response Capability
Today, an organization’s maturity is measured by its response capability, and a failure in the security domain is a clear sign of organizational immaturity. Such failures can destroy trust and reputation within minutes, while also putting the company’s very survival at risk.
This is compounded by the lack of key protocols for the moment an incident occurs and for how a company should act when infiltration can no longer be avoided. In this regard, the report emphasized that, just as fire drills exist, companies must have response protocols for cyber or security incidents.
Improvisation in the face of a ransomware attack, for example, not only halts operations but also extends recovery time, which can average between four and five months — a timeframe that can be considered an eternity for a retail business, for instance.
What Companies Must Do to Avoid Closure
In this scenario, preventing a cybersecurity incident from leading to a company’s closure requires moving from words to action. The first step is to accept that an attack is inevitable and that the difference between survival and failure lies in the level of preparedness.
Having full visibility of the infrastructure through continuous monitoring and early detection tools makes it possible to identify threats before they escalate. This must be complemented by clearly defined response protocols that establish roles, responsibilities, and key decisions during an incident, thus avoiding improvisation.
Ongoing staff training, especially in detecting fraud and social engineering attacks, drastically reduces attackers’ points of entry.
Finally, conducting cyber incident simulations — in the same way that fire drills are conducted — strengthens response capabilities, shortens recovery times, and protects any organization’s most valuable asset: business continuity and customer trust.











