Centralized Identity Management
Author: David Lanz. Passionate about technology and customer service, I add value through my knowledge to help organizations achieve their goals and objectives, using technology as an enabling pillar.
March 27, 2025.
Centralized Identity Management is a core aspect of efficient Cybersecurity management in organizations.
Are you considering acquiring a tool that gives you the opportunity to streamline your digital transformation, positioning yourself as one of the leaders in your sector? Are you thinking about implementing centralized identity management in your organization as a tool to reduce costs, streamline processes, and increase customer satisfaction?
In a dynamic business environment characterized by agility and the constant improvement of both internal and external customer experience, the adoption of modern Customer Identity and Access Management (CIAM) solutions is a differentiating element of strategic priority, not only as a technological trend but as an indispensable pillar for your company’s success.
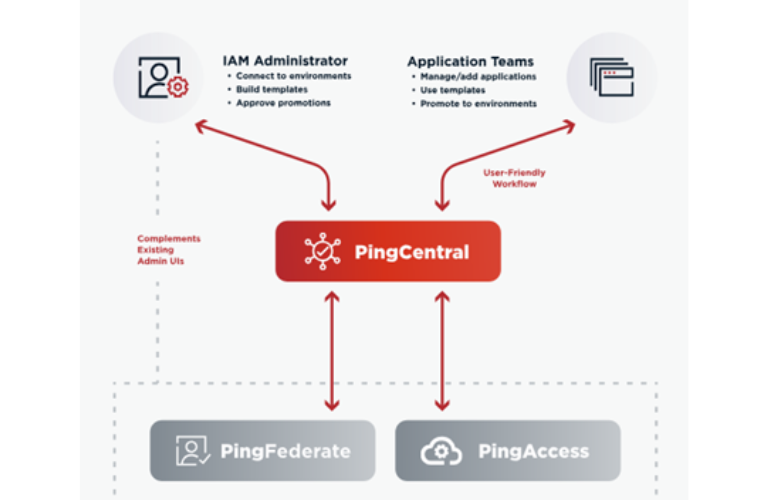
In this context, solutions like Ping Identity © are recognized by Gartner, Forrest, among others, as one of the best and most powerful options available in the intelligent identity management solutions market, offering a detailed guide on how to accelerate CIAM administration to improve both security and customer experience.

Key Benefits (Organizational Impact)
- Simplicity: Ping Identity provides a single, easy-to-use administration console, while being robust enough to cover multiple needs, optimizing time and resources.
- User-friendly and efficient navigation interface: Reduces the number of clicks required to perform fundamental management tasks through intuitively designed consoles that allow administrators to focus on key strategies without wasting time navigating or trying to decipher unnecessarily complex configurations.
- Adaptability: Ping Identity stands out for its ability to replicate specific architectures of any environment without setbacks or cumbersome processes.
- Compliance with standards: Ping Identity is based on standardized cybersecurity protocols such as OAuth 2.0, OpenID Connect, and SAML, ensuring not only its interoperability in different environments but also minimizing vulnerability risks.
- Pre-configured and customizable tools: Combines ready-to-use interfaces with the ability to be customized, achieving a perfect balance between a fast implementation process and the generation of a unique management experience adaptable to each business.
Practical Applications:
- Simplify user registration and access processes: Reducing/eliminating cumbersome identity management processes, providing the administrator with a single management console, while providing the end-user with a user-friendly tool for self-management of their access keys.
- Improve security: Through advanced Multi-Factor Authentication (MFA) configurations and permission management in each of the IT environments.
- Optimize internal resources: Minimizing the time spent by system administrators on repetitive/recurring administrative tasks.
- Comply with privacy regulations: Through centralized management of personal data, significantly reducing the dispersion and multiplicity of users’ personal information.
Finally, Ping Identity, in addition to being a tool for the digital transformation of organizations, provides a strategic and intelligent approach to centralized identity management, allowing companies to modernize their operations, improve their customer experience, and ensure compliance with high global security standards.











